In a stark revelation that highlights the growing intersection of cyber-espionage and domestic criminal collaboration, the U.S. Department of Justice (DOJ) announced on Wednesday the sentencing of two American citizens for their pivotal roles in a sophisticated, state-sponsored remote IT worker scheme. The operation, which effectively funneled American corporate resources and salaries directly into the coffers of the Democratic People’s Republic of Korea (DPRK), serves as a sobering reminder of the vulnerabilities inherent in the modern, decentralized workplace.
Matthew Isaac Knoot of Nashville, Tennessee, and Erick Ntekereze Prince of New York were sentenced to a combined total of three years in federal prison. Their convictions mark a significant milestone in the U.S. government’s ongoing effort to dismantle the illicit revenue streams sustaining the North Korean regime’s nuclear and ballistic missile programs.
Main Facts: The Anatomy of a Deception
The scheme relied on a deceptively simple premise: exploiting the trust inherent in remote hiring processes. North Korean operatives, posing as highly skilled IT professionals, systematically applied for remote work positions at various U.S. companies. Leveraging falsified identities, forged credentials, and high-quality deepfake video conferencing, these operatives successfully bypassed initial human resources screenings.
Once hired, the companies followed standard industry protocols by shipping company-issued hardware—specifically high-performance laptops—to the "employees" to facilitate their work. This is where Knoot and Prince entered the operation. Acting as "laptop farm" operators, they received these devices at their private residences.
Instead of the hardware going to the supposed remote workers, it was plugged into KVM (Keyboard, Video, Mouse) switches at the homes of the American collaborators. This allowed the North Korean operatives to log into the corporate networks from overseas while appearing, via IP masking and the physical presence of the laptop, to be working from a domestic U.S. location. The collaborators effectively turned their living rooms into remote-access hubs, allowing DPRK state actors to embed themselves within the digital infrastructure of unsuspecting American firms, ranging from Fortune 500 companies to smaller tech startups.
Chronology of a Coordinated Effort
The investigation, spearheaded by the FBI and the Department of Justice, uncovered a multi-year effort that operated with high levels of organizational discipline.
- The Inception (2020–2021): As the COVID-19 pandemic forced a global shift to remote work, North Korean operatives saw an opening. Intelligence reports suggest the regime began scaling up its "IT worker" program, training thousands of workers in specialized coding and development to operate from hubs in China, Russia, and Southeast Asia.
- The Recruitment Phase (2022): Investigative documents reveal that Knoot and Prince were recruited through online forums and encrypted messaging platforms. They were tasked with setting up "farms" that would act as the physical anchor for the foreign actors.
- The Operation (2023): During this period, the laptops were in constant operation. The collaborators provided the physical infrastructure, ensuring the machines remained connected to the internet and responding to corporate IT support requests.
- The Crackdown (Early 2024): Federal investigators began tracking suspicious traffic patterns and logistical anomalies related to hardware shipments. Digital forensic evidence linked the domestic IP addresses to the remote-access logins used by the North Korean operatives.
- The Sentencing (October 2024): Following guilty pleas, the DOJ handed down the final sentencing, bringing a formal end to these specific cases while signaling that investigations into the wider network remain active.
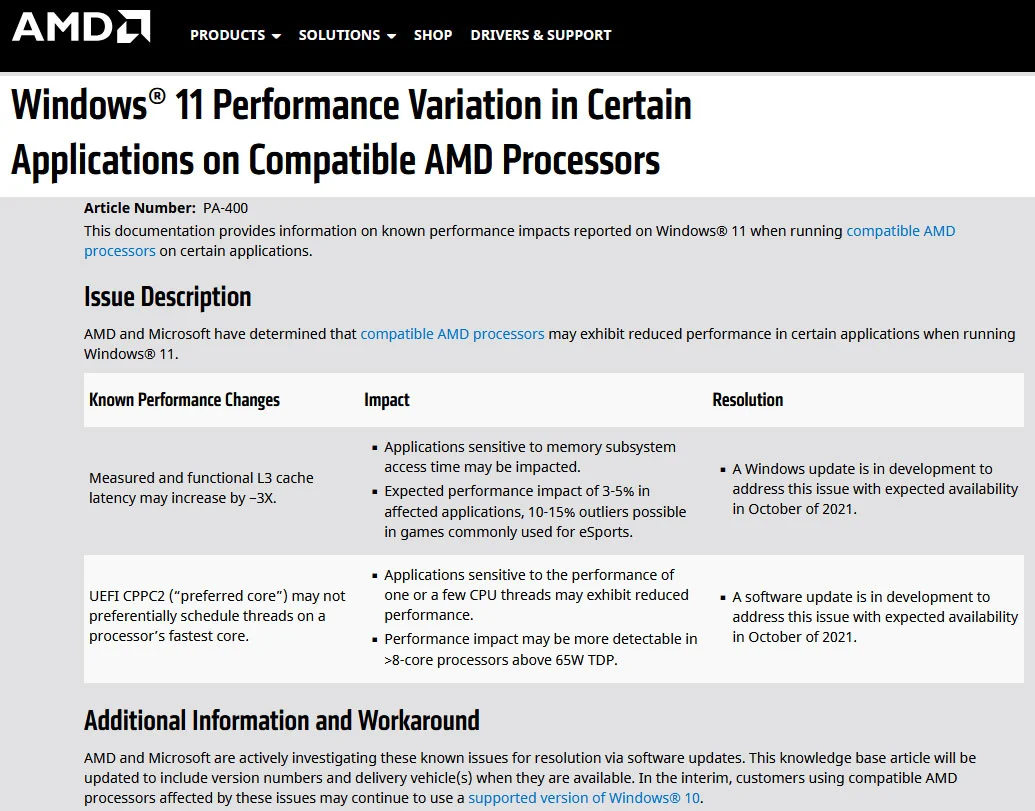
Supporting Data: The Scale of the Threat
The financial implications of this scheme are profound. Estimates provided by the U.S. Treasury Department suggest that North Korean IT workers generate hundreds of millions of dollars in annual revenue for the regime. By securing high-paying roles in the U.S. tech sector, these operatives were often able to earn six-figure salaries, the vast majority of which were sent back to the DPRK to support state-sanctioned weapons proliferation.
Furthermore, the operational security (OPSEC) risks are unprecedented. By granting these operatives legitimate network credentials, companies unknowingly provided them with:
- Network Access: Potential backdoors into sensitive proprietary data and intellectual property.
- Internal Intelligence: Access to internal communication channels, allowing foreign actors to understand corporate culture, product roadmaps, and security protocols.
- Credential Harvesting: The ability to use compromised corporate accounts to launch secondary attacks or further infiltrate other third-party vendors within the supply chain.
Security analysts note that this is not merely "fraud." It is a strategic effort to embed state-sponsored actors inside the "nervous system" of the American economy.
Official Responses and Federal Oversight
The Department of Justice has been clear in its messaging: those who facilitate these schemes, whether knowingly or through willful blindness, will face the full weight of federal law.
"These sentences demonstrate that the U.S. government is actively identifying and dismantling the networks that allow North Korean operatives to exploit our corporate infrastructure," said a spokesperson for the DOJ. "Companies have a responsibility to conduct rigorous background checks, but they are also victims of a highly sophisticated form of social engineering that targets the very nature of remote work."
The FBI has issued renewed guidance for corporations, emphasizing the need for "identity verification during the hiring process," the use of hardware-based security keys, and monitoring for anomalous login times and geographical locations. The Bureau warned that the "laptop farm" model is likely evolving, with operatives increasingly using more advanced techniques to hide their true locations.
Implications: The End of the "Trust-Based" Hiring Era
The fallout from these cases is already changing the landscape of the tech industry. HR departments are moving away from traditional remote onboarding, opting instead for more stringent identity verification services, including biometric checks and live, proctored interviews that require applicants to show their physical environment.
The Erosion of Remote Trust
The most significant implication is the erosion of trust in the remote hiring model. For years, the tech sector prided itself on being borderless, hiring the best talent regardless of geography. The North Korean IT scheme has weaponized this ethos. Companies are now implementing stricter "geo-fencing" for employee logins, which, while necessary for security, may inadvertently stifle the global diversity and flexibility that remote work once championed.
Corporate Accountability
There is also an ongoing debate regarding corporate negligence. Should a company be held liable for failing to detect a sophisticated deepfake operation? Legal experts suggest that while the primary fault lies with the North Korean regime and the domestic collaborators, firms that fail to perform basic due diligence on hardware shipping locations could face increased scrutiny from federal regulators.
A Geopolitical Security Crisis
Ultimately, the sentencing of Knoot and Prince underscores that cybersecurity is no longer just a technical issue—it is a geopolitical one. When an American company hires an IT worker, they are now being forced to consider whether their payroll is inadvertently funding an ICBM program. The "laptop farm" model has been dismantled in these two instances, but the broader threat remains.
As the digital front lines of global conflict shift from server rooms to the home offices of ordinary Americans, the responsibility for securing the enterprise has never been higher. The lesson for the private sector is clear: in an era of sophisticated digital warfare, the physical location of the worker—and the integrity of the hardware they use—is the first, and perhaps most important, line of defense.