For digital marketing agencies, the nightmare usually begins with a notification that seems mundane: "Your access to this asset has been restricted."
For the client, this is a betrayal of trust. They hired you precisely so they wouldn’t have to worry about the technical volatility of Meta’s ecosystem. When your agency’s Business Manager is restricted, you aren’t just dealing with a software bug—you are managing a professional crisis. You have built robust access workflows, onboarded a talented team, and scaled your operations just as a growing agency should. Yet, somewhere in the shadows of Meta’s security infrastructure, an automated system has analyzed your team’s login patterns and concluded that your agency is not a legitimate business—it is a security breach.
This is the central irony of modern agency life: Your agency’s legitimate operations are mathematically indistinguishable from a coordinated fraud ring in the eyes of Meta’s security AI.
The Anatomy of a False Positive
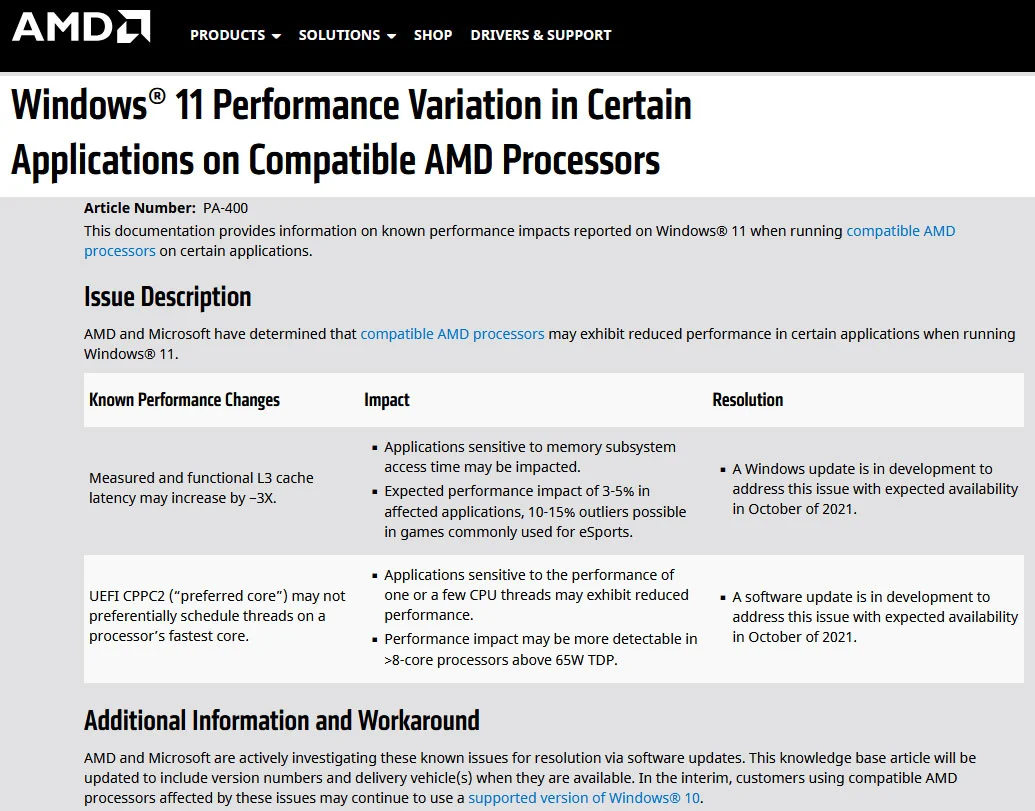
Meta’s security architecture is built on a binary premise: legitimate user behavior is consistent and predictable, while anomalous behavior is malicious. Its AI monitors for specific triggers: logins from disparate geographic locations, multiple IP addresses accessing the same asset simultaneously, and the sudden introduction of new administrative devices. (Meta Transparency Center, 2026).
For a solo brand manager, these signals are indeed red flags for a hacked account. But for an agency, this describes a "normal Tuesday." Your team is likely remote, logging in from different cities, utilizing various networks, and switching between personal devices and office hardware. When multiple staff members access client accounts from a shared agency office IP address, they inadvertently mimic the exact behavioral signature used by professional fraud syndicates running "black hat" campaigns across stolen assets (Multilogin Academy, 2026).
Meta’s system does not have a native category for "agency." It only recognizes patterns. Because your agency’s operations align perfectly with the "malicious actor" pattern, the platform’s security enforcement is not a malfunction—it is the system performing exactly as designed.

The Domino Effect: Why Portfolio Restrictions are Fatal
Most agencies operate under the false impression that a restriction is limited to a single Ad Account or a specific Page. The reality is far more dire. A Business Manager restriction is a systemic, portfolio-level event.
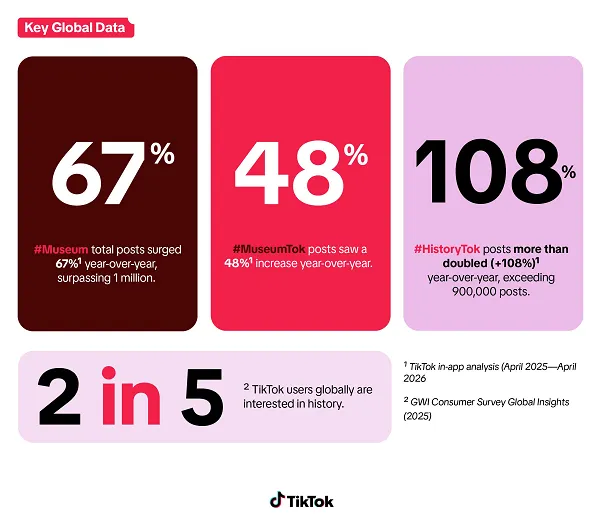
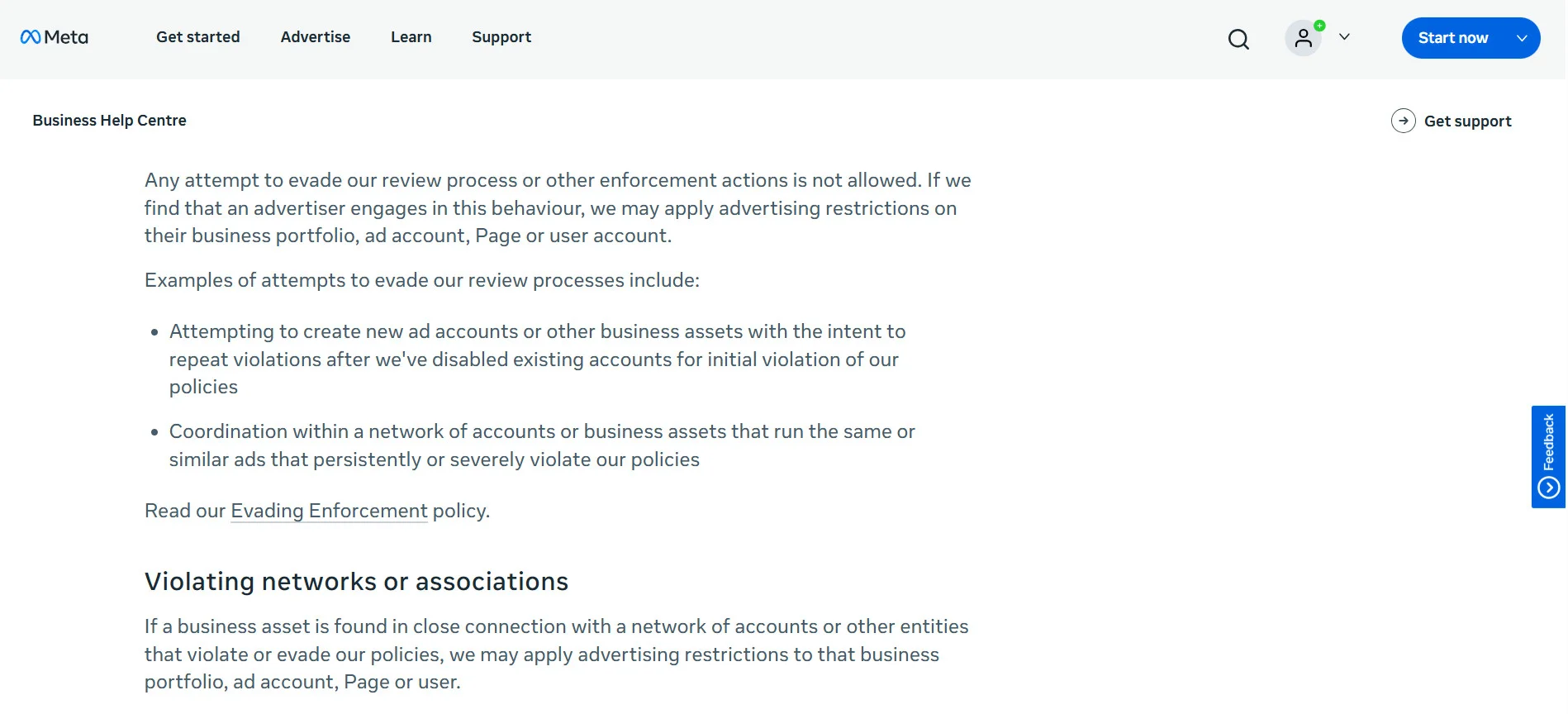
When Meta flags a Business Manager, the consequences are cascading. Every asset tied to that container—every ad account, every pixel, every Instagram handle, and every payment method—is effectively paralyzed. Per Meta’s internal enforcement guidance, once the Business Manager is compromised, every user associated with that manager loses access, regardless of their individual account standing (Meta Business Help Center, 2026).
If you manage ten clients through one Business Manager, a single login discrepancy doesn’t just affect one client; it triggers a ten-client blackout.
The Illusion of Recourse
The most frustrating aspect of this process is the appeal mechanism. As noted by industry observers, "You cannot appeal a login ban from behind a login screen." (Mojo Dojo, 2026). Because the enforcement is automated at scale, the path to a human reviewer is virtually non-existent for standard agency restrictions.
Even when agencies attempt to provide the "gold standard" of verification—government IDs, birth certificates, and biometric face scans—they often find their accounts banned again within hours. This is because the underlying behavioral trigger (the login pattern) has not changed. You are proving who you are, but you are not proving why the system is flagging your activity.
The Root Cause: A Broken Onboarding Culture
The fundamental issue is that the official solution provided by Meta—Partner access, granular role-based permissions, and credential-free asset sharing—is rarely used in the field.
In theory, Meta’s Business Manager allows agencies to manage client assets without ever touching a client’s password. In practice, however, these systems are notoriously cumbersome. Agencies operate on tight deadlines. During a client’s onboarding sprint, waiting for a client to navigate five layers of non-obvious settings to grant "Partner access" can delay a campaign by a week.
Sharing a password takes thirty seconds. It is an operational shortcut that has become an industry standard. However, this shortcut is the primary driver of the credential-sharing pattern that Meta’s security AI is specifically programmed to hunt down. The workaround, intended to save time, is the very thing creating the structural risk.
The Strategic Shift: Moving Outside the Detection Layer
To survive in the current ecosystem, agencies must change their philosophy: If you cannot change Meta’s AI, you must stop feeding it data it can misinterpret.
The goal is to remove your team from Meta’s direct login detection layer. This is where third-party social media management platforms become essential. Tools that connect to Meta via OAuth do not require your team to log into Meta’s interface directly. Instead, they connect to Meta’s API once, establishing a trusted, verified application relationship (Meta for Developers, 2026).
When your team publishes content through a tool like SocialPilot, Meta receives a request from a single, verified application. Because your team is not logging in individually, there are no individual login events to trigger the "hacker" flags. Your agency’s workflow becomes invisible to the security AI because the platform sees one consistent, authorized source managing the account.
Operational Workflow Comparison
| Task | Where It Happens | Risk Level |
|---|---|---|
| Post Scheduling/Publishing | SocialPilot Dashboard | Near Zero |
| Content Calendar Management | SocialPilot Dashboard | Near Zero |
| Client Approvals | SocialPilot Dashboard | Near Zero |
| Analytics/Reporting | SocialPilot Dashboard | Near Zero |
| Ad Campaign Setup | Meta Ads Manager | Moderate (requires Partner access) |
| Pixel/Audience Setup | Business Manager | Moderate (requires Partner access) |
By segregating daily tasks (publishing, reporting, approvals) into a third-party platform and reserving Meta’s native interface only for high-level technical tasks—and only through formal Partner access—you isolate the risk.
Implementing the "Risk-Free" Protocol
Agencies that successfully navigate this environment follow a strict four-step protocol:
- Credential Audit: Identify every team member with direct password access to client accounts. Treat these as "toxic assets."
- Formalize Partner Access: For tasks that must happen in Business Manager (e.g., Pixel setup, Ads configuration), ensure only one designated administrator uses official Partner access. No password sharing.
- Migrate to OAuth Publishing: Connect all social channels via OAuth through a reputable management platform. This effectively removes the "login event" from Meta’s detection radar.
- Revoke Direct Access: Once the new workflow is established, strip all individual team members of direct administrative passwords.
The Reality Check: Meta Isn’t Changing
It is a mistake to view these restrictions as a bug that Meta will eventually "fix." The platform was built for brands managing their own identities—single teams, single locations, and predictable, linear behavior. Agencies, which operate as decentralized, multi-location hubs, were never the primary use case.
Meta’s security system is doing exactly what it was designed to do: protecting the platform from unauthorized access. The agencies that have thrived in the last few years are those that stopped waiting for Meta to build a "special" agency mode and instead adopted a "zero-trust" workflow.
By removing your team from the login detection layer, you aren’t just bypassing a technical hurdle; you are professionalizing your agency’s security posture. In a world where a single automated flag can destroy a client relationship, the only reliable position is one that is invisible to the machine.