In an unprecedented move that underscores the growing intersection between home networking and international espionage, the FBI and the National Security Agency (NSA) have confirmed that thousands of home and small-office wireless routers across the United States have been systematically compromised by Russian military intelligence.
Following a court-authorized intervention that saw federal agents remotely reboot and reset thousands of infected devices, officials are now issuing a stark warning: the intervention was merely a temporary stopgap. For the vast majority of users, the only path to true security is the immediate retirement and replacement of aging, vulnerable hardware.
Main Facts: The "Fancy Bear" Incursion
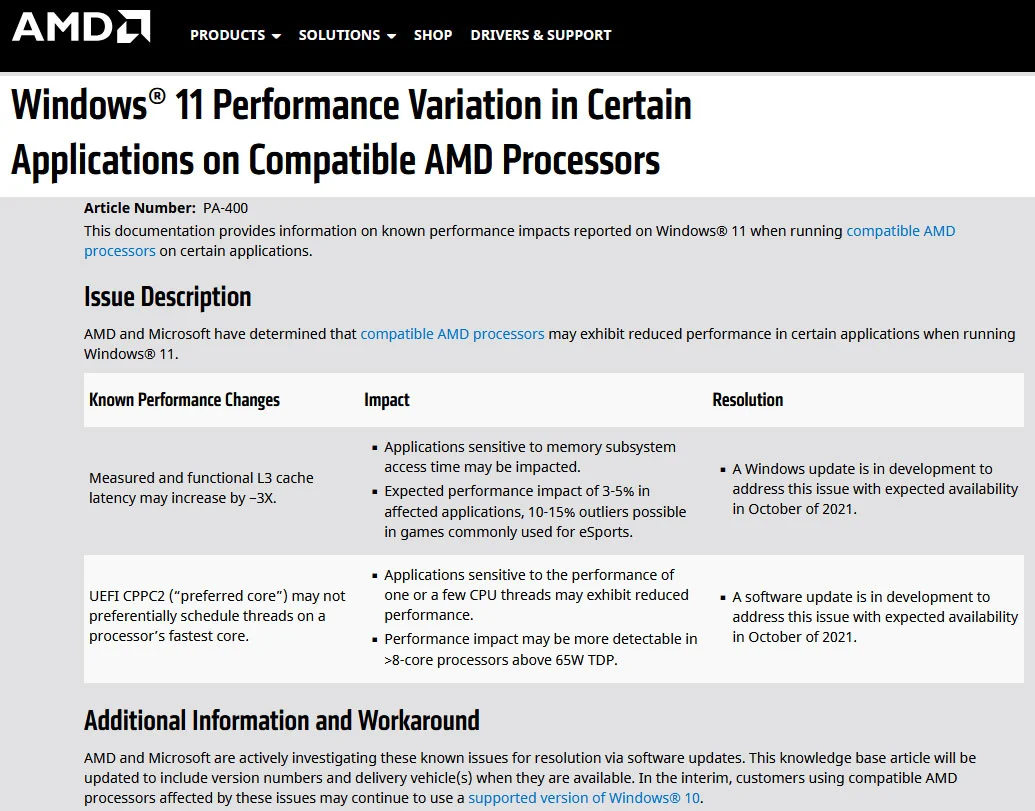
The breach is attributed to the GRU—Russia’s military intelligence directorate—and specifically to the elite hacking unit known as APT28, or "Fancy Bear." According to a joint advisory released by the FBI, NSA, and international partners, these actors have been leveraging vulnerabilities in legacy router firmware to infiltrate networks since at least 2024.
By exploiting unpatched security flaws, the hackers gained unauthorized access to private networks, effectively turning unsuspecting household routers into a distributed proxy network. Once inside, the attackers were able to intercept sensitive communications, harvest authentication tokens, and scrape login credentials, effectively granting them a "man-in-the-middle" position on the user’s own network.

The FBI took the extraordinary step of obtaining a court order to remotely reach out to these compromised devices. By forcing a reboot of these routers, federal agents were able to disrupt the malicious processes running in the devices’ volatile memory. However, the agencies stress that because the underlying security vulnerabilities remain unpatched on these obsolete machines, the hackers can—and likely will—re-infect the devices unless the hardware is physically replaced.
Chronology of a Digital Siege
The campaign represents a sophisticated, long-term effort to maintain persistence within Western infrastructure.
- Early 2024: Intelligence agencies begin observing anomalous traffic patterns originating from home-grade routers, tracing the activity to APT28 infrastructure.
- Late 2024–Early 2025: The scale of the compromise expands as Russian actors move from targeting government entities to broad-spectrum "smash and grab" operations against small businesses and home users.
- April 7, 2026: The FBI and NSA make a formal, public disclosure of the campaign. The agencies announce that they have executed a court-ordered remote intervention to "cleanse" infected hardware.
- Mid-April 2026: Security researchers and the UK’s National Cyber Security Centre (NCSC) identify that the primary targets are legacy TP-Link models and other routers that have reached their "End of Life" (EOL) status, meaning they no longer receive security patches.
- Present Day: Cybersecurity experts and federal officials are urging a "rip and replace" strategy, warning that firmware updates are no longer a viable defense for these specific models.
Supporting Data: Why Legacy Hardware is the Weakest Link
The core of the issue lies in the life cycle of consumer-grade networking equipment. Many users treat routers as "set and forget" appliances, often keeping them in service for a decade or more. However, as hardware ages, manufacturers cease the development of security patches.
The specific models identified by the FBI often date back to hardware architectures from as early as 2007. When a router is no longer supported, any discovered vulnerability—such as an overflow error or a flaw in the remote management interface—becomes a permanent backdoor.

The NCSC has corroborated the FBI’s findings, noting that the attackers utilized a custom modular malware framework designed to survive a standard power cycle. While the FBI’s remote reset disrupted this, it did not—and could not—remove the root cause: the software code on the device is fundamentally broken, and there is no manufacturer update to fix it.
Official Responses: The Federal Stance
The joint statement from the FBI and NSA marks a shift in how federal agencies interact with domestic network infrastructure. In the past, government intervention in private property was largely limited to criminal prosecution. Here, the FBI acted as a "digital janitor," proactively sanitizing the network to prevent further espionage.
"We are dealing with a threat that is persistent and indifferent to the target," a federal cybersecurity official noted during the briefing. "When an adversary is capable of pivoting from a home router into a corporate network or a government teleworker’s machine, every individual device becomes a node of national security interest."
The agencies have explicitly advised that simply resetting the password is not enough. "If your device is listed as an unsupported legacy model, you are essentially driving a car with no brakes," the advisory suggests. "No amount of caution can compensate for a structural flaw in the machine itself."

Implications for the Future of Home Security
The ramifications of this event are twofold: they redefine the "threat surface" of the modern home, and they force a re-evaluation of how we manage "smart" infrastructure.
1. The Rise of the "Disposable" Router
We have entered an era where networking hardware must be viewed as having a finite expiration date, much like a laptop or a smartphone. If a router is no longer receiving security updates from the manufacturer, it is a liability. Consumers are encouraged to check their manufacturer’s website for the "End of Support" date and plan for hardware replacement every 4–6 years.
2. The Dangers of Remote Management
One of the primary vectors used by APT28 was the "Remote Management" feature found in many router admin panels. This feature is intended to allow IT professionals to troubleshoot networks from afar, but in the hands of a home user, it often remains enabled with a weak, default password. The FBI strongly advises that all users navigate to their router’s admin dashboard and ensure this feature is disabled immediately.
3. VPNs and Encryption as a Last Line of Defense
For remote workers, the threat is magnified. When a router is compromised, the traffic flowing through it—even if the website uses HTTPS—can be subjected to DNS hijacking or metadata analysis. The FBI recommends that remote workers employ a Virtual Private Network (VPN) at all times. By encrypting traffic at the device level (the laptop or phone), the VPN ensures that even if the router is compromised, the data passing through it remains indecipherable to the eavesdropper.

4. Hardening the Home Network
Beyond replacing the hardware, users are urged to adopt "security by design" habits:
- Automatic Updates: Always enable automatic firmware updates in the router settings.
- Credential Hygiene: Never use the default username/password printed on the sticker under the router. Change these to a unique, complex passphrase immediately upon installation.
- Segmentation: Modern routers allow for "Guest Networks." By isolating IoT devices (smart bulbs, fridges, cameras) onto a guest network, users can prevent a breach in a low-security smart device from jumping to their main work computer.
Conclusion: A Wake-Up Call
The FBI’s remote intervention was a temporary victory in a much larger, ongoing conflict. As state-sponsored actors continue to scan the global internet for vulnerable entry points, the humble home router has become a strategic asset in the theater of cyber warfare.
For the average consumer, the message is clear: check your hardware status today. If you are using a router that has reached its end-of-life, the risk of interception is no longer theoretical—it is a proven reality. The cost of a new, modern router is a small price to pay for the security of your private data, your professional communications, and the integrity of your personal network.
In this new landscape of digital threats, ignorance is not just bliss—it is an open door for foreign intelligence services. Take the time to audit your home setup, update your security protocols, and if necessary, retire your aging hardware. Your digital privacy depends on it.