The digital infrastructure of global education faced a profound reckoning this week as Canvas, the ubiquitous learning management system (LMS) utilized by thousands of academic institutions, fell victim to a sophisticated cyberattack. The timing could not have been more catastrophic: the incident coincided with the peak of the spring finals season, a period when millions of students rely exclusively on the platform for examination delivery, grade submissions, and critical academic communication.
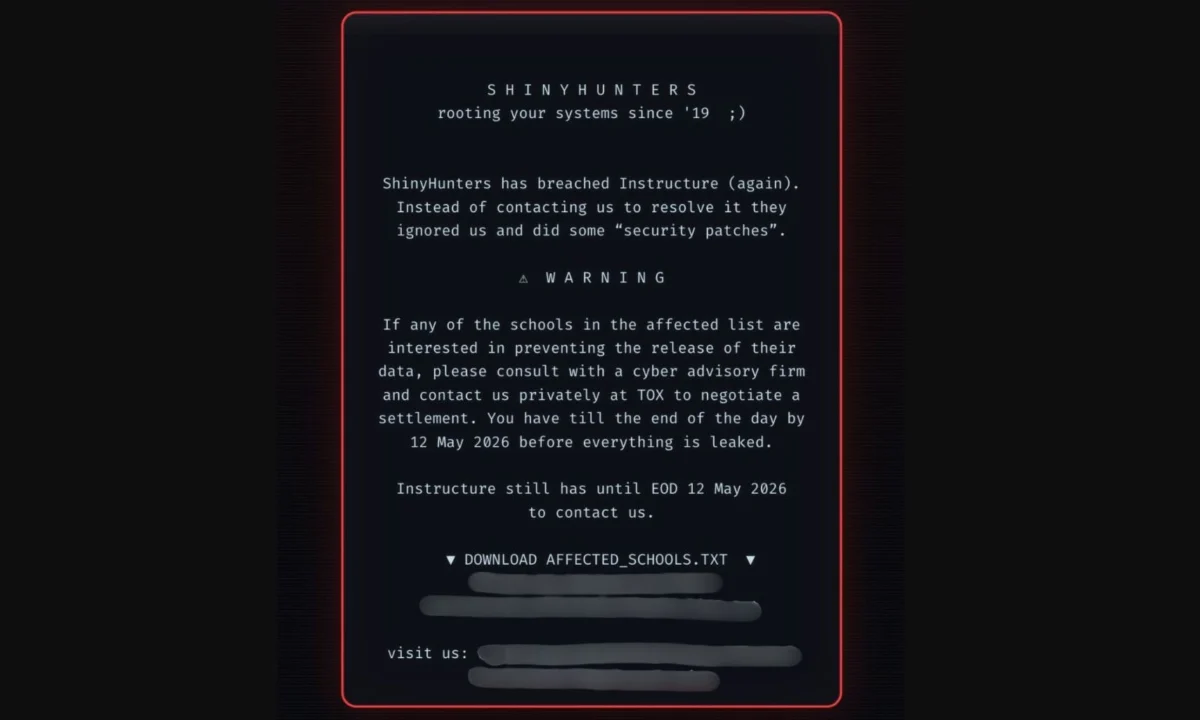
As login portals across the globe were defaced with ominous ransom demands, the academic world was thrust into a state of chaos. The incident has been attributed to the notorious hacking collective "ShinyHunters," a group with a long history of high-profile data breaches. The breach has not only highlighted the fragility of our centralized digital learning ecosystems but has also ignited a firestorm of debate regarding the security protocols of educational technology providers.
The Chronology of the Breach: A System Under Siege
The crisis began to unfold as thousands of students and faculty members reported "403 Forbidden" errors or were greeted by an unauthorized ransom message upon attempting to access their Canvas portals. Instead of their usual dashboard, users encountered a stark warning from ShinyHunters, claiming that the group had breached Instructure—the parent company behind Canvas—and had successfully exfiltrated a massive cache of user data.
According to cybersecurity monitoring reports, the initial defacement occurred in a coordinated "mass-login" campaign. The hackers left a digital footprint that included a hard deadline: May 12, 2026. The message warned that unless specific extortion demands were met, the stolen data—allegedly containing information on millions of students, teachers, and staff members—would be published on the dark web.
Instructure’s incident response team moved to take the platform offline shortly after the breach was detected. The company identified the entry point as an exploit involving its "Free-for-Teacher" accounts. This specific vector allowed the attackers to bypass standard authentication hurdles, granting them a foothold in the system. While the platform was returned to service in stages, the damage to the academic calendar was already done.
Understanding the Adversary: Who is ShinyHunters?
ShinyHunters is not a novice operation; they are a sophisticated, profit-driven cybercriminal syndicate that has previously targeted corporate titans such as Ticketmaster and Rockstar Games. Their modus operandi typically involves the theft of massive databases followed by a high-stakes extortion attempt.
This is not the group’s first interaction with Instructure. In September 2025, ShinyHunters successfully infiltrated Instructure’s Salesforce environment, employing social engineering tactics to gain access to internal business systems. At that time, Instructure issued a statement asserting that while business contact details were compromised, the core product data—the Canvas LMS itself—remained secure. The recent May 2026 attack, however, represents a significant escalation, as it directly impacted the live environment and the personal data of the platform’s end-users.

Supporting Data and Scope of the Breach
While Instructure has been quick to reassure the public that financial records and account passwords were not part of the exfiltrated dataset, the reality of the breach remains significant. Reports suggest that the stolen information includes:
- Full names of millions of students and faculty members.
- Institutional email addresses.
- Unique student identification numbers.
- Internal messaging logs and administrative metadata.
For the cybersecurity community, this information is a goldmine for secondary attacks. The exposure of internal messaging logs, in particular, poses a severe risk. These logs allow attackers to craft highly convincing, context-aware phishing emails. An attacker could, for instance, pose as a department head or a specific professor, referencing actual class names or assignments to trick students into clicking malicious links or divulging further personal information.
Official Responses and Institutional Fallout
The impact on the ground was immediate and disruptive. As the outage persisted, universities and school districts were forced to implement emergency continuity plans. Many institutions chose to postpone final examinations, while others shifted to physical paper exams or alternative third-party communication tools.
In an official statement, Instructure acknowledged the gravity of the situation: "We take the security of our users’ data with the utmost seriousness. Upon discovering the unauthorized access, we immediately initiated our security protocols, engaged third-party cybersecurity forensic experts, and worked to isolate the compromised systems."
Despite these efforts, the silence from the company regarding the specific nature of the ransom negotiations has fueled speculation. Recent activity on the dark web indicates that Instructure has been removed from the ShinyHunters "Pay or Leak" portal. While some analysts interpret this as a sign that a resolution or negotiation has occurred, others warn that it may simply mean the attackers are moving to a private extortion phase away from the public eye.
The Broader Implications: A Wake-Up Call for EdTech
The Canvas outage serves as a chilling reminder of the "single point of failure" risk inherent in modern education. By centralizing assignments, grades, and communication into a single digital platform, institutions have gained significant efficiency but have also created a massive target for threat actors.
1. The Erosion of Digital Trust
The primary casualty of this event is the trust placed in educational technology providers. Students and faculty, already under the pressure of finals, found themselves betrayed by the very tool designed to support them. When a primary learning environment goes dark, it disrupts the cognitive and social processes of learning, leaving students feeling vulnerable and exposed.

2. The Need for "Defense in Depth"
The fact that a "Free-for-Teacher" account could serve as the gateway to a massive breach suggests that security was not sufficiently segmented. Cybersecurity experts argue that EdTech firms must move toward a "zero-trust" architecture, where internal systems are segmented to ensure that an exploit in one module does not lead to a total platform compromise.
3. The Necessity of Contingency Planning
Educational institutions have long prioritized digital transformation, but they have often lagged in digital resilience. The chaos of the past week proves that "backups" cannot just mean data recovery; they must include operational continuity plans. Schools must maintain the capability to pivot to analog or decentralized methods of examination and communication when the primary digital infrastructure fails.
Looking Forward: Protecting the Future of Learning
As the academic community recovers from this crisis, the focus must shift from reactive patching to proactive defense. The threat of secondary attacks, such as phishing campaigns, remains high in the weeks following the breach. Institutions should warn their students to remain vigilant, to ignore unsolicited emails regarding their grades or accounts, and to enable multi-factor authentication (MFA) wherever possible.
Ultimately, the ShinyHunters incident is a watershed moment for the EdTech industry. It forces a conversation about the responsibilities of platforms that hold the keys to the future of millions. While innovation in learning management is vital, it must be matched by an equal commitment to security. As we move further into a digital-first academic world, the ability to protect the sanctity of the classroom—both physical and virtual—is no longer an optional feature; it is an absolute necessity.
The May 2026 breach will likely result in increased regulatory scrutiny for providers like Instructure and a renewed push for strict data privacy standards in schools. For now, the students and teachers affected by the outage must navigate the aftermath, hoping that the sensitive data stolen by the attackers is not used to further jeopardize their academic or professional lives. The lesson is clear: in an age of constant connectivity, the most important technology a school can invest in is the one that keeps its students safe.