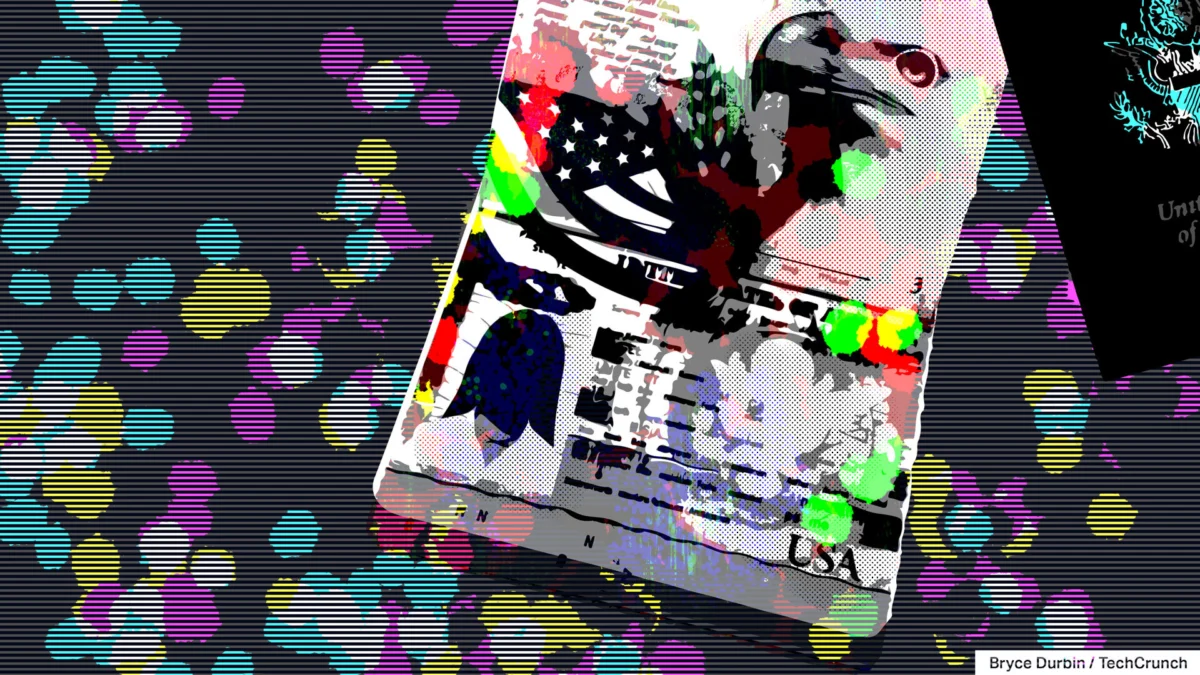
In a stark reminder of the fragile state of digital privacy in the age of automated verification, more than one million sensitive documents—including passports, driver’s licenses, and biometric selfie verification photos—were left openly accessible on the public web. The data, belonging to international travelers who used the “Tabiq” hotel check-in system, was exposed due to a fundamental misconfiguration in a cloud storage bucket.
The breach was brought to light by independent security researcher Anurag Sen, who discovered the vulnerability earlier this week. The system is maintained by Reqrea, a Japan-based technology startup that provides facial recognition and document-scanning kiosks to hotels across the country. Following an inquiry from TechCrunch, the company moved to secure the data, but the incident has already ignited a firestorm of concern regarding the risks associated with “Know Your Customer” (KYC) protocols and the handling of government-issued identity documents by third-party vendors.
The Anatomy of the Lapse: How a Simple Error Exposed Millions
The breach originated from a publicly accessible Amazon Web Services (AWS) S3 bucket. In cloud computing, an S3 bucket is a storage container where companies house files, databases, and application data. While these buckets are configured to be private by default, they can be made public through manual settings or administrative oversight.
In this instance, the bucket—appropriately, yet dangerously, named “tabiq”—was configured to allow anyone with a web browser to view, download, and harvest its contents without the need for authentication or a password. This meant that any individual who discovered the bucket’s existence could potentially scrape millions of high-resolution images of government identification.
“This was not the result of a sophisticated state-sponsored cyberattack or a complex exploit,” noted security analysts. “It was a classic, avoidable case of human error.”
The exposure was so significant that it was indexed by GrayHatWarfare, a search engine that tracks publicly accessible cloud storage buckets. The index revealed that the bucket contained files dating back as far as early 2020, suggesting that the sensitive data had been sitting unprotected for years.
Chronology of the Discovery and Remediation
The timeline of the exposure and the subsequent scramble to secure the data highlights the vital role of independent researchers in maintaining the safety of the internet ecosystem:
- 2020 – 2026: The “tabiq” storage bucket is misconfigured, likely during initial setup or a subsequent update, making it public to the internet. During this time, the system accumulates a massive repository of passports, licenses, and facial recognition data from international guests.
- Early Week (Current): Security researcher Anurag Sen identifies the exposed bucket while auditing public cloud instances. Recognizing the severity of the data contained within—specifically, the PII (Personally Identifiable Information) of travelers from around the globe—he notifies the relevant authorities and the press.
- Mid-Week: TechCrunch contacts Reqrea and the Japan Computer Emergency Response Team (JPCERT).
- Post-Disclosure: Upon being alerted to the breach, Reqrea immediately restricts access to the S3 bucket, ending the public exposure.
- Ongoing: The company initiates an internal investigation, working with legal counsel to determine the extent of the unauthorized access and the notification process for affected individuals.
The Mechanics of Modern Verification and Its Flaws
The Tabiq system represents a growing trend in the hospitality and service industries: the automation of identity verification. By utilizing facial recognition and automated document scanning, companies like Reqrea aim to streamline the check-in process, reducing wait times and human error at the front desk.
However, these systems inherently require the collection of the most sensitive data an individual possesses. When a guest scans their passport, the system does not just verify the identity; it creates a digital footprint that is often stored in cloud environments.
The incident with Reqrea is not an isolated event. It follows a pattern of “data leakage” that has become a systemic issue. Just recently, the Canadian money transfer service “Duc App” faced a similar crisis after misconfiguring an Amazon server, exposing the documents of its users. Furthermore, a high-profile breach at Hertz last year saw the theft of driver’s license information for over 100,000 customers.
These events challenge the narrative that automated verification is inherently “safer” than human verification. While a human front-desk clerk might misread a name, they do not typically store a million identity documents in an unsecured, public digital warehouse.
Official Responses and Corporate Accountability
In the wake of the exposure, Reqrea has been forced to confront the potential legal and reputational fallout. Masataka Hashimoto, a director at Reqrea, provided a formal statement to TechCrunch acknowledging the situation.
“We are conducting a thorough review with the support of external legal counsel and other advisors to determine the full scope of exposure,” Hashimoto stated. He confirmed that the company is currently reviewing server logs to determine whether any malicious actors accessed the data during the years it was public.
A critical question remains: Why was the bucket made public? Amazon has spent the better part of the last decade implementing safeguards to prevent exactly this type of human error. The platform now issues multiple warning prompts when a user attempts to change an S3 bucket’s status from “private” to “public.” This suggests that the error at Reqrea was not merely an accidental click, but a deliberate (though perhaps misunderstood) configuration choice that bypassed these built-in safety barriers.
Reqrea has pledged to notify affected individuals, though the sheer volume of data—spanning several years—presents a massive logistical challenge in terms of identifying every guest who had their information compromised.
Broader Implications: The “Identity Crisis” of the 21st Century
The Reqrea incident provides a chilling case study for the risks inherent in our increasingly digitized society. As governments move toward stricter age-verification laws and private companies adopt “Know Your Customer” mandates, the demand for individuals to upload sensitive, government-issued documents to third-party servers is reaching an all-time high.
1. The Vulnerability of Biometric Data
Perhaps most concerning is the exposure of “selfie verification” photos. Unlike a password or a credit card number, which can be changed if compromised, biometric data and official identity document details are essentially permanent. Once a passport image is leaked, it can be used for identity theft that lasts a lifetime.
2. The Failure of Best Practices
The cybersecurity industry frequently emphasizes “best practices”—the foundational, boring, yet vital habits that keep data secure. These include encryption at rest, principle of least privilege, and regular security audits. The Reqrea breach underscores that even when companies deploy sophisticated AI-driven software, they can still be undone by a failure to perform the most basic tasks, such as checking an access control list on a storage bucket.
3. The Future of Regulation
This incident is likely to increase the pressure on regulators in Japan and abroad to enforce stricter penalties for companies that handle sensitive data with such negligence. As the debate over global age-verification laws continues to intensify, experts are increasingly warning that the infrastructure required to support these laws is currently too insecure to handle the burden of mass surveillance and data collection.
4. The Role of Search Engines like GrayHatWarfare
The fact that tools like GrayHatWarfare exist highlights the double-edged sword of the modern internet. While these databases are useful for security researchers like Sen to identify and alert companies to leaks, they also serve as a directory for malicious hackers seeking easy targets. The transparency of the web, once its greatest strength, has become a significant liability for organizations that fail to secure their digital borders.
Conclusion: A Wake-Up Call
The exposure of one million identity documents is a stark reminder that the digital transformation of our daily lives is outpacing our ability to secure the data it generates. Hotels, banks, and startups alike are effectively becoming custodians of our most private information, yet many operate with a level of digital hygiene that is fundamentally mismatched with the value of the data they hold.
For the guests whose passports and photos are now floating somewhere in the digital ether, the damage may already be done. For the tech industry, the lesson is clear: no amount of artificial intelligence or sophisticated automation can compensate for the lack of fundamental cybersecurity diligence. As we move further into a future where our physical identity is tied to our digital footprint, the cost of these “minor” human errors will only continue to rise.